If your idea of studying is to watch back-to-back videos or even read a book from start to finish, or if you have ADHD and you can’t sit still long enough to get past 3 videos before needing a break, then the next two videos are for you.
While I’ve never gone in to get diagnosed for ADHD, I have an extremely hard time sitting still and watching videos or reading for long periods of time. So I’ve had to find techniques that work for me, and I hope they also work for you.
Or again, if you’re planning on sitting there watching 30 videos back-to-back, in the end, you won’t remember concepts from the first 20.
Or, if you just write down quick notes from each lecture and you later just try to read back through them, you won’t remember 90% of what you’ve read by the time you’re done.
Don’t just watch videos back to back and take notes. That is not effective studying.
In this video, I’ll share tools that can help you stay on track with your studies and that can make notetaking, or your studying in general, more effective.
In the next lesson, I’ll share more insights into scientifically proven study techniques to increase your attention.
Oh also, this video is not sponsored by anyone or any company, so if I mention any products by name, it’s because I’ve personally used them and I personally found them helpful. I also don’t have any affiliate links or anything like that. What matters most is that you find tools that work best for you, and that may not always be the same tools that I use.
Notetaking tips
Let’s talk about notetaking.
I am not a paper and pencil kind of guy. I’ve heard the studies that say it’s typically better, and frankly I still don’t care. My handwriting is absolutely awful so I can’t re-read my notes half the time, it looks super messy, and it takes so much longer that I don’t have the patience for it.
Instead, the best tool that I’ve found for writing notes to this day is Notion. Notion has sponsored huge YouTube channels for a while now (I’m not sponsored, though) so I’m sure you’ve heard of it and there are plenty of tutorials out there, but as you can see here, I use it extensively. I use it to create my courses, and I also used it to study for the exam.
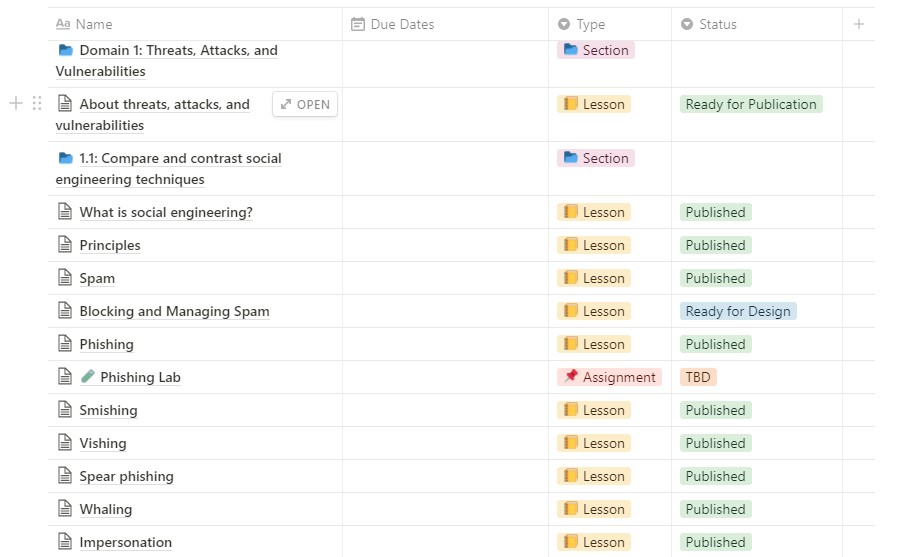
I’ve also made this study template available for you to use. You can copy it (top right corner) and make it your own!
Again, I’ll talk a bit more about notetaking strategies in the next video, for now, let’s focus on the tools.
So if you’re good with paper and pencil, then that’s a great approach. The only downside here is that you won’t be able to search your notes later on, unless you upload them to something that takes your notes and transcribes them. I’ve never tried that kind of software before, but I heard it can be pretty good.
If you’re more of a digital notetaker like I am, use a tool like Notion to take more structured notes. This is such a large exam with so many concepts that if you just dump all your notes in one document, it will get messy really fast.
Pomodoro Technique
Next, let’s talk about staying focused on your studies. If you have ADHD or something similar, this, I think, will help you a lot if you don’t already do it.
I have been using what’s called the Pomodoro Technique on days that I have a very hard time focusing. So it’s not every day, but pretty close to it.

One of the hardest parts is getting started. You procrastinate because all of a sudden you remember 10 other things that you’re supposed to have done already, like maybe cleaning your desk, doing the dishes, vacuuming, or whatever else. Before you know it, 2 hours have gone by, and you still haven’t studied a thing.
One main reason this happens is that we’re overwhelmed with the idea of what comes ahead. We subconsciously think that studying is going to be super tough, and so our brains don’t want to get started.
However, the Pomodoro Technique helps reduce that feeling by giving concrete start and stop times. It’s essentially a time management system that separates your tasks into specific periods of time.
Usually, or by default, sessions are 25 minutes long with 5 minutes breaks.
So when you start the clock, you already know that you’re only going to be studying for 25 minutes. That tells your brain that it really won’t be so bad, because after that 25 minutes, you’ll have a break. Then, after 4 of these sessions, you get an even bigger break — typically 15 to 20 minutes.

Personally, I don’t like the 5 minutes breaks. The 25 minutes works fine for me, because that’s usually long enough to focus on a task intensely and then after that I usually need a break, but 5 minutes isn’t even enough time for me to stand up and walk around. So instead, I take 10 minutes break in between each 25 mins session, and then my longer break is 20 minutes.
That gives me enough time to walk around or pull up a YouTube video for some entertainment, and then I feel like I’m ready to get back to studying.
Experiment with times to see what you personally prefer, but if you’re not currently using the Pomodoro Technique, I highly, highly recommend it.
There are many free apps out there that you can put on your phone, or you can also use browser ones like I do and just have a background window that’s running the timer.
Tell family, friends, colleagues, etc…that you will be inaccessible for the next 25 minutes
Along the same lines, it’s really important that you tell your family, friends, colleagues, or whoever else you need to tell, that you will be inaccessible for the next 25 minutes.
At a minimum, put your devices on “Do Not Disturb,” although some people will benefit from turning their devices off completely. I’m serious — turn your phone off if you find yourself constantly checking it.
As long as you give people a timeframe of when you’ll be available again, I’ve found that this usually helps out a bunch.
Get a good pair of noise-canceling headphones
If you can afford to, I also highly recommend getting a good pair of noise-canceling headphones, and put on music without any lyrics. There are great studying playlists available on YouTube that you can pop on while you study, and these help me tremendously.
The noise cancelation helps you get immersed in your studies and in the music, and it avoids distractions that are coming in from the outside world.
Sometimes even just a distant loud car exhaust can break my focus, but a good pair of noise cancelation headphones can tune out most of those distractions.
I personally use the Sony headphones and really enjoy them, but I’ve recently picked up a pair of DT 770 Pros for audio editing, and not only do they sounds absolutely incredible with music, but they also do a fantastic job of blocking outside sounds even without any noise cancelation.

Join a community. It increases your odds of passing!
Another recommendation is that you join a community. Obviously, I’d love for you to join Cybr’s Discord community by going to cybr.com/discord, but what matters most is that you find other members who are also studying for the exam. Maybe they’re a little bit more experienced than you are, or they’re ahead with their studies. Either way, having someone that will hold you accountable — even indirectly — will work wonders.
This is the same as if you were to go to the gym by yourself versus with a gym partner. While some people can stay self-motivated, many need to have that external driver to keep showing up day-in and day-out.
The same applies to studying. If it’s just you, you’ll be more likely to slack or take the day off. If you’ve got someone else also studying and keeping track, then that will motivate you to push through even when it gets tough.
So this one really is a no-brainer.
Stay healthy while you’re studying
Last, but certainly not least, stay healthy during this time! A lot of people will stop going to the gym, or they’ll let studying cut into their sleeping time.
That’s the absolute worst time for you to be doing that!
There are countless studies that prove that physical exercise helps with mood, creativity, and memory. All 3 of those are important to helping you pass your exam, so you don’t want to lose that.
The same holds true for sleep. If you don’t sleep enough, your brain literally cannot retain information as well. So that extra studying you’re doing that’s cutting into your sleep is actually doing more harm than good.
Instead, plan your studies ahead of and create a solid schedule, and that way you won’t have to cut into your sleep schedule.
Conclusion
Alright, that’s it for now. I didn’t even mean for the video to go on this long, but these are super important topics that I truly believe will help increase your odds of passing the exam, so don’t lose track of them as you go on with your studies.


Great content. I’d not heard of ‘Notion’, looks to be a very useful piece of software, I’ll definitely give it a try and ‘Yes Please’ to the course content notion template.
Glad my recommendation was helpful then! I will definitely plan on making the Notion template available, though please give me a few days as I need to clean it up and make it ready for sharing 🙂
Here you go for the notion template! https://cybr.notion.site/CompTIA-Security-SY0-601-Ultimate-Study-Template-3fbe57dd879b4e8b9dd1d17a344049e7
It’s still a work in progress so I welcome all feedback