Get Started Using SQLMap for SQL Injection Pentesting
SQLMap is a popular open-source penetration testing tool used to detect and exploit SQL injection vulnerabilities. In prior posts, we looked at general concepts of SQL, we learned the basics of SQL injection techniques, and we looked at 8 SQL injection cheat sheets. Now, it’s time to learn how to get started using SQLMap.
What is SQLMap?
SQLMap, as stated, is a pentesting tool specifically designed to detect and exploit SQL injection vulnerabilities. While it’s a relatively simple tool to use, it does include powerful features that aren’t as commonly found in other SQLi-related tools. Some of those features are designed to gather information, while others are designed to completely compromise databases, and in some cases, also take over database servers.
It’s able to offer all of this functionality with a powerful detection engine, features that include database fingerprinting, fetching data from a database, accessing the underlying file system, and executing commands on the operating system via out-of-band connections.
SQLMap is developed in Python which makes it highly portable and compatible with most environments. In fact, it’s included in many GNU/Linux distributions, such as Kali Linux.
In a nutshell, SQLMap is able to:
- Identify vulnerable parameter(s)
- Identify which SQL injection techniques can be used to exploit the vulnerable parameter(s)
- Fingerprint the back-end database management system
- Attempt to enumerate data or takeover the database server as a whole
Since we already covered different attack techniques, we won’t go into details again, but here are the techniques supported by this tool:
- Boolean-based blind
- Time-based blind
- Error-based
- UNION query-based
- Stacked queries
Of course, this post would not be complete without mentioning the creators and authors:
Now that we have an overview understanding of what SQLMap is, let’s get to work!
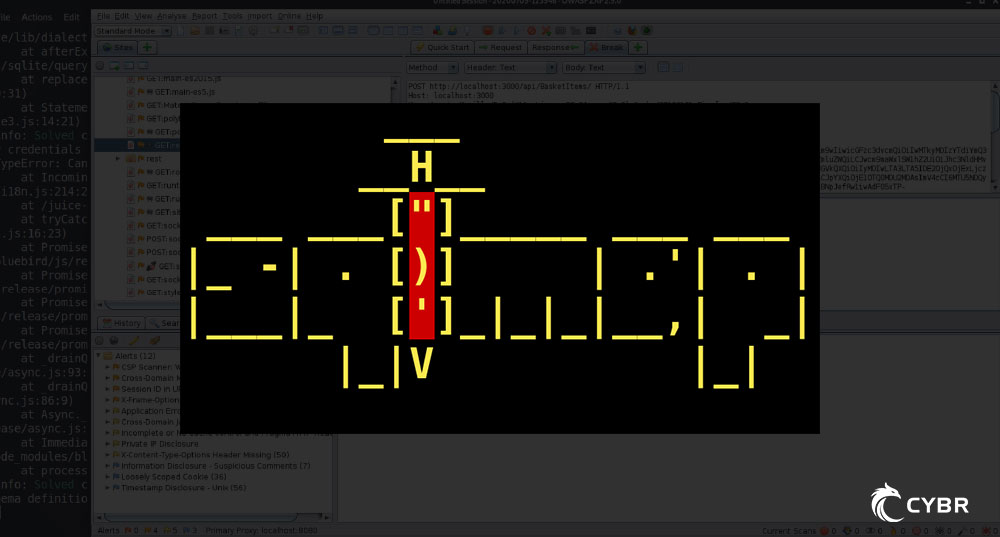
Creating a test environment
When trying out penetration testing tools, you should never use them on real/production resources. For one, unless you have explicit written permission to do it, you could get into legal trouble. Second, these tools can be destructive. Data could be compromised or modified. databases could become corrupted, etc…
So for all these reasons, we need to first create an isolated test environment. This doesn’t have to take a long time, and we have blog posts that explain exactly how to get started. If you don’t already have a test environment, go complete the steps in this article first: Install Kali on VirtualBox: The quickest way.
Once you’ve completed those steps, you can move on to the next!
Get started using SQLMap
Using a distribution that includes SQLMap by default
As mentioned, SQLMap is included, by default, in certain distributions — especially if they are distros meant for penetration testing. If you followed the steps from our prior section, then you will have Kali Linux installed in your new environment. Kali is one of those distros that include SQLMap my default, so no more steps are required.
Install SQLMap manually
If you didn’t follow the prior steps for setting up an environment because you already have one set up, but your distribution doesn’t include SQLMap by default, or if you want to manually install it for whatever other reason, you can certainly do that.
Download the latest archive here. Then, use unzip to extract that archive from where it was downloaded.
Once extracted, go into its directory, and you will be able to use SQLMap with Python.
To get a list of basic options:
python sqlmap.py -hCode language: CSS (css)To get a list of all available options:
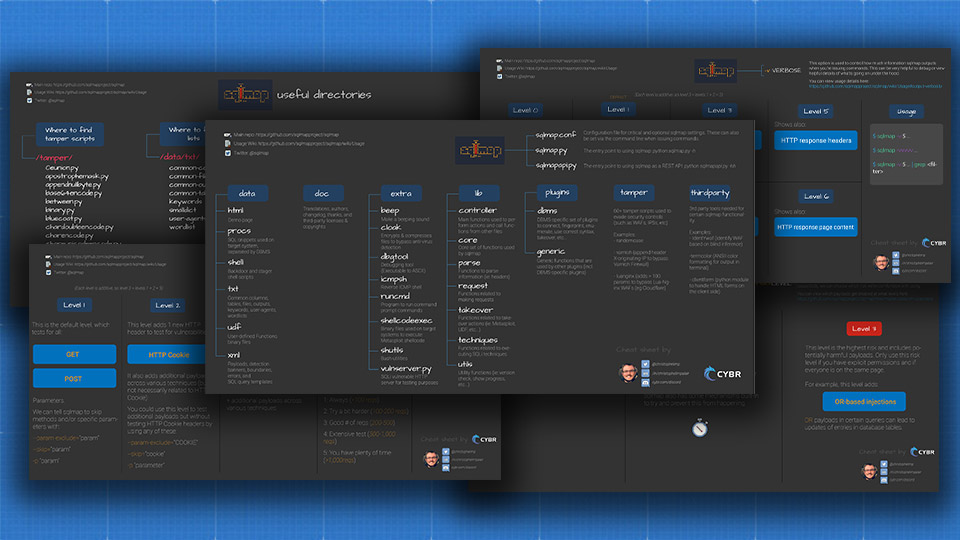
python sqlmap.py -hhCode language: CSS (css)SQLMap options
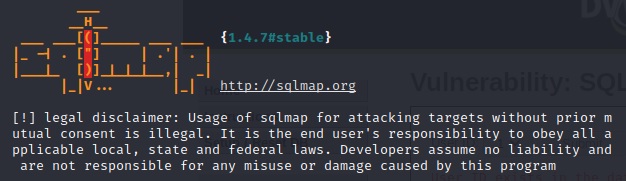
sqlmap -h
___
__H__
___ ___[,]_____ ___ ___ {1.4.7#stable}
|_ -| . [)] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
Usage: python3 sqlmap [options]
Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: 0-6 (default 1)
Target:
At least one of these options has to be provided to define the
target(s)
-u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-g GOOGLEDORK Process Google dork results as target URLs
Request:
These options can be used to specify how to connect to the target URL
--data=DATA Data string to be sent through POST (e.g. "id=1")
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--random-agent Use randomly selected HTTP User-Agent header value
--proxy=PROXY Use a proxy to connect to the target URL
--tor Use Tor anonymity network
--check-tor Check to see if Tor is used properly
Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts
-p TESTPARAMETER Testable parameter(s)
--dbms=DBMS Force back-end DBMS to provided value
Detection:
These options can be used to customize the detection phase
--level=LEVEL Level of tests to perform (1-5, default 1)
--risk=RISK Risk of tests to perform (1-3, default 1)
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
--technique=TECH.. SQL injection techniques to use (default "BEUSTQ")
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables
-a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--passwords Enumerate DBMS users password hashes
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate
Operating system access:
These options can be used to access the back-end database management
system underlying operating system
--os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC
General:
These options can be used to set some general working parameters
--batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target
Miscellaneous:
These options do not fit into any other category
--sqlmap-shell Prompt for an interactive sqlmap shell
--wizard Simple wizard interface for beginner usersCode language: PHP (php)While there are a ton of options, here are some of the ones I recommend you start with understanding.
General options
-u– the target URL--cookie– HTTP cookie information--data– data to send through the POST request-p– specify testable parameters (ie: if you’re wanting to test the “ID” parameter, you would do -p id)--dbms– if you know the DBMS powering the application, you can specify it here instead of SQLMap trying to figure it out--batch– chooses the default options instead of prompting for user’s input when there are decisions to be made during command execution
For example, if you have a target URL that you’d like to test at http://localhost/vulnerabilities/sqli_blind/, you would use:
sqlmap -u "http://localhost/vulnerabilities/sqli_blind/"Code language: JavaScript (javascript)If that endpoint relies on cookies and POST data to make a successful request, we can add that information, like this:
sqlmap -u "http://localhost/vulnerabilities/sqli_blind/" --cookie="id=10; PHPSESSID=39qedittgtbc7rfsm69gjvidl0; security=medium" --data="id=1&Submit=Submit" -p id
Code language: JavaScript (javascript)Enumeration
-a– retrieve all the information possible-dbs– enumerate DBMS databases--current-user– retrieve the current DBMS user--current-db– retrieve the current DBMS database--passwords– enumerate DBMS users password hashes--tables– enumerate DBMS database tables--columns– enumerate DBMS database table columns--schema– enumerate the DBMS schema
(Enumerate, by the way, simply means to find and list out the information)
With our prior request, if we wanted to list out the databases, we could tag on -dbs:
sqlmap -u "http://localhost/vulnerabilities/sqli_blind/" --cookie="id=10; PHPSESSID=39qedittgtbc7rfsm69gjvidl0; security=medium" --data="id=1&Submit=Submit" -p id --dbs
Code language: JavaScript (javascript)Operating system access
--os-shell– prompt for an interactive operating system shell--os-pwn– prompt for an OOB (out-of-band) shell, Meterpreter, or VNC. SQLMap has some features that work well with Meterpreter for post exploitation
For a complete breakdown of all options, check out the wiki.
SQLMap in action
Now that you learned how to get started using SQLMap, move on to this article: How to set up the DVWA on Kali with Docker. Those steps will help you install Docker on your new Kali environment, and then it will show you how to start the Damn Vulnerable Web Application environment, which is what we will use to play around with SQLMap.
So once you have installed the DVWA, go to this post and start attacking it: Blind SQL injections with SQLMap against the DVWA.






Responses